Insight Blog
Agility’s perspectives on transforming the employee's experience throughout remote transformation using connected enterprise tools.
7 minutes reading time
(1317 words)
What is a SAST Tool and Why Do You Need It?
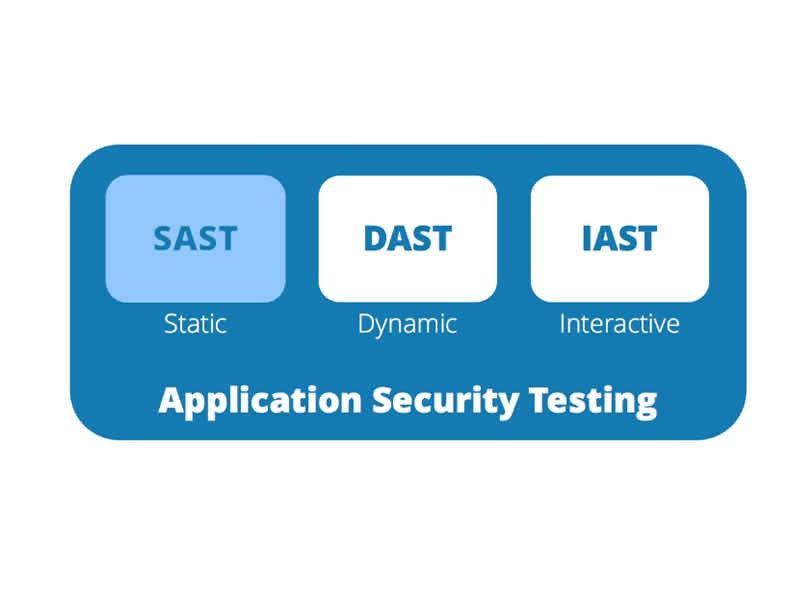
Static Application Security Testing (SAST) is a frequently used Application Security (AppSec) tool, which scans an application's source, binary, or byte code.
One problem takes hold of every software business—maintaining a safe and secure source code, and providing a solution for this issue may involve prioritizing security. Vulnerabilities and risks threaten the business with less visibility, which should be a stepping stone toward every solution. That is alongside knowing how to deal with identified security challenges, emphasizing cybersecurity's importance.
But lo and behold, a toolkit like Static Application Security Testing (SAST) exhibits a novel way of identifying these risks and vulnerabilities, ensuring that security is the top priority from the idea to the deployment of the application.
How Does SAST Provide a Solution to Security Problems?
This static analysis has far-reaching consequences that touch every line of code written for every app. It analyzes the program's source code in search of vulnerabilities that hackers could use to launch an attack on the company's computer network. White-testing refers to analyzing source code for security flaws before compilation, which is what this SAST tool does.
The Importance of SAST: Testing Works Goes a Long Way in Securing each Development
As one of the best options in security testing that can be very adaptable and present at every stage of the Software Development Life Cycle (SDLC), it is possible that programmers can have a close look at their codes each time they write them because the integration of security into their Integrated Development Environment (IDE) is present at all times.
SAST occurs relatively early in the SDLC since it does not require an already-functioning application and may be performed without code execution. This enables fixes for security flaws to be implemented early in development before they can cause build disruptions or introduce new security holes into the final product.
The Global Market of SAST Predicts Progression
According to the MarketsandMarkets 2023 Market Forecast, the Development, Security, and Operations (DevSecOps) market is expected to be worth $5.9 billion in five years, growing at an annualized pace of 31.2% from 2018. This finding is supported by Grand View Research, which predicts a market value of $10.7 billion by 2025, nearly double what was anticipated for 2023.
These statistics suggest that small-to-large scale businesses, especially those involved in application and software development, should prioritize security in each aspect of their process. Here are more reasons why businesses need static analysis for security.
#1. Rapid, Precise, and Risk-Free Program Deployment
Automatic monitoring for every line of code by SAST technologies helps detect and repair security vulnerabilities far faster than human-performed robust code reviews.
This means to imply that down from the start of the initially planned concepts to its product deployment, security is guaranteed and integrated into the building blocks of code within the application, which is crucial to maintaining safety measures against risks.
Problem-Solution Approach Provided by SAST ToolThe many automated SAST systems that have emerged over the years and been proven effective in practice are now standard practices for all businesses. These automated tools must keep an eye on the code at all times. Once automated testing results are in, security vulnerabilities can be easily located, fixed, and valuable insights gained.
Debug times can be reduced with the use of SAST tools.
#2. Moving Security to the Left Implies Securing the Preparation Stages
Security can be built in from the beginning if SAST is used early in the software development lifecycle. This allows them to detect problems with the code early in the development process when they are more easily fixed. Delaying security measures raises the likelihood that exploits will be introduced into the production system.
Prevention of Potential Dangers in the SDLCThe risk and cost of fixing vulnerabilities are reduced when security is shifted to the left. SAST can analyze both client and server-side security issues. Application security testing helps reduce the complexity of risk mitigation by identifying vulnerabilities in the source code or binaries.
Imagine that, during live-fire evaluation, vulnerabilities are discovered. If you find vulnerabilities early on in the SDLC, you can implement fixes to mitigate their impact before continuing with development.
#3. Low-Cost Method for Detecting and Addressing Security Issues
With SAST tools, developers may get instantaneous feedback on their code and fix any issues before passing it on to the next phase of the SDLC. Doing so may assure us that security issues won't be disregarded. Since vulnerabilities are already detected and fixed before moving on to the next level, the budget is terminated immediately. By addressing all potential issues at once, financial strain is avoided.
The Economic Value of SAST's Proactive Security Monitoring and MaintenanceMost security flaws and defects are introduced during development. Therefore, finding them early can have a significant financial impact. The use of SAST results in economic, time, and material savings. According to their findings, reducing the typical number of incidents has a positive financial impact.
The savings from just one project are estimated to be hundreds of thousands of dollars.
#4. Using a SAST Tool Simplifies Reporting and Risk Monitoring
With SAST tools, developers may create custom reports that can be viewed offline, exported and tracked via dashboards. To quickly address the tool's security flaws and get their apps into production with minimal hiccups, developers must keep meticulous records of the tool's findings. As a result of this process, companies will get closer to having a secure SDLC.
Visual Representation of the Issue Aid in Finding a SolutionThere is also the option of making a cause and effect diagram out of the issues uncovered by SAST tools. This helps deciphers the code. Using these tools, we can quickly identify insecure code and inspect it in detail to determine its weak points. Agencies can provide comprehensive advice on correcting issues and the optimal place in the code to fix them without requiring an in-depth understanding of the security domain.
Moreover, it emphasizes the Knowledge Management Framework and Methodology that tries to understand its importance to be detailed in implementing a solution within the business.
#5. Validating Code Safety using SAST to Ensure Secure Coding
To ensure the safety of any application, whether it be web, desktop, mobile, or embedded, secure code must be developed. Computer hackers easily find ways to take advantage of poorly constructed software. Such an assault could result in several adverse outcomes, including denial of service, data loss, leakage of sensitive information, damage to end-user software and systems, and harm to your company's brand reputation.
Where Can SAST Make Use of Code Security?
Emphasizing static analysis' point and root, SAST can be used to check it before it's written for more secure and risk-free code. Before putting code into production, it helps ensure that it has been developed following specific safe coding standards.
#6. Evidence Suggests that Using Different SAST Tools Increase the Effectiveness of Each
Examining SAST as a part of a human-driven security assessment process for an open-source e-government project was the focus of the research into the prevalence of static analysis in software security evaluation.
Consider the Consequences Learn About Innovative Methods for Testing Cybersecurity
The study detailed how specialists in the security industry select, evaluate, and combine SASTs into a novel method for assessing software security. Semi-structured interviews have been used to conduct an initial evaluation of the approach. The results suggest that while some SAST tools perform better than others, considerable gains can be made by combining multiple such instruments.
This shows that the current effort to analyze the safety of open-source software could benefit from a combined effort comprising different SAST implementations.
In Summary, Using SAST is an Essential Step Toward Enhancing Security
Now that you understand what SAST is and how it may aid your company, it's time to put your newfound knowledge to use. By integrating SAST into the SDLC and the continuous integration process, you can safeguard the business from security threats and the ever-changing security landscape.
Categories
Blog
(2970)
Business Management
(372)
Employee Engagement
(223)
Digital Transformation
(191)
Growth
(142)
Intranets
(136)
Remote Work
(63)
Sales
(53)
Collaboration
(48)
Customer Experience
(30)
Culture
(29)
Knowledge Management
(28)
Project management
(28)
Leadership
(20)
Comparisons
(9)
News
(1)
Ready to learn more? 👍
One platform to optimize, manage and track all of your teams. Your new digital workplace is a click away. 🚀
Free for 14 days, no credit card required.