Insight Blog
Agility’s perspectives on transforming the employee's experience throughout remote transformation using connected enterprise tools.
10 minutes reading time
(1910 words)
Strategies and Best Practices for Protecting Sensitive Data while Working Remotely
Companies of all sizes are under attack. So how do your apply Best Practices for Protecting Sensitive Data while Working Remotely?
Organizations of all sizes are currently facing various threats. Concurrently, the adoption of remote work has become imperative for modern businesses seeking to attract skilled professionals and establish strategies for seamless operations.
An excellent illustration of effective business continuity unfolded during the spring of 2020, as companies worldwide swiftly transitioned hundreds of thousands of employees to remote work in response to the COVID-19 (coronavirus) pandemic.
With all its benefits, working remotely requires being highly attentive to the security of your own and your client's data. While you think no one would care about your business, the statistics indicate that over the past 2022 year, there have been 443 million people, who suffered from data compromises in the US.
To ensure data security, you should follow a comprehensive approach consisting of different practices and techniques that help prevent data leaks.
When working remotely, ensuring the security of files and protecting against malware is of paramount importance. The distributed nature of remote work introduces vulnerabilities that malicious actors may exploit.
Inadequate security measures or lapses in employee awareness can lead to unauthorized access, data breaches, and the infiltration of malware.
Remote workers must prioritize secure file storage, utilizing encrypted platforms and robust authentication protocols.
Regular software updates, reliable antivirus software, and cautious email and web browsing habits are essential to mitigate malware risks.
Educating employees about potential threats and implementing strict security protocols are crucial steps to safeguard sensitive information and maintain a secure remote work environment.
Unfortunately, things can slip through the net, and you can still end up with malware on your Mac. If this has happened to you, read on for advice about How to get rid of malware on Mac?.
What Is Data Security About?
Imagine how much data you store on your computer: your personal data with all the passwords to the accounts and business data that refers to clients' names, credit card information, phone numbers, and other sensitive details.
- Data security refers to the protection of digital information from unauthorized access, use, disclosure, alteration, or destruction.
- It involves implementing measures to ensure the confidentiality, integrity, and availability of data.
- Confidentiality ensures that data is accessible only to authorized individuals or entities and remains private.
- Integrity ensures that data is accurate, consistent, and reliable by preventing unauthorized modification, deletion, or tampering.
- Availability ensures that data is accessible and usable by authorized users whenever needed, while safeguarding against service disruptions or downtime.
- Authentication mechanisms, such as passwords, biometrics, or multi-factor authentication, verify the identity of users and prevent unauthorized access.
- Encryption transforms data into a secure format using algorithms, making it unreadable to unauthorized individuals or systems.
- Encrypted email provider services add an extra layer of security by ensuring that all communications are protected with encryption, preventing unauthorized access to sensitive information in transit or at rest.
- Firewalls and network security protocols protect data by monitoring and controlling network traffic, preventing unauthorized access or malicious activities.
- Backup and disaster recovery strategies create copies of data and establish processes to restore it in the event of data loss or system failure.
- Access control mechanisms limit user privileges and permissions, ensuring that individuals can only access data relevant to their roles or responsibilities.
- Regular software updates and patch management help address vulnerabilities and security weaknesses in operating systems and applications.
- Intrusion detection and prevention systems (IDPS) monitor networks and systems for potential security breaches, detecting and mitigating threats in real-time.
- Security audits and assessments evaluate the effectiveness of security controls, identify vulnerabilities, and recommend improvements to enhance data security.
- Employee training and awareness programs educate personnel about data security best practices, policies, and potential risks, fostering a security-conscious culture.
- Compliance with legal and regulatory requirements, such as the General Data Protection Regulation (GDPR) or Health Insurance Portability and Accountability Act (HIPAA), ensures data security and privacy in specific industries or jurisdictions.
If you neglect to apply a measure to pretect data and the prevention from cybercrimes, it can end up ruining your organization.
Data security is crucial for every worker: whether you are a CEO of a company or a customer support agent. And the most widely spread reason why data compromises happen is because of negligence.
The studies show that 90% of data breaches occur only because an employee dont take data security seriously.
Best Techniques to Stay Safe as a Remote Worker
If you are a remote worker or have a team working from home, these strategies will help you build solid protection from any typical cybercrime.
Here are some of the best techniques to stay safe as a remote worker when it comes to data security:
- Avoid using public Wi-Fi networks and opt for a virtual private network,
a VPN, to
encrypt your internet traffic and protect your data from interception.
- Implement 2FA for your online accounts whenever possible. This adds an extra layer of security by requiring a second verification step, such as a code sent to your phone, in addition to your password. We will go in to more details on this later
- Regularly update your operating system, antivirus software, and other applications to patch security vulnerabilities and protect against the latest threats. Regularly update your operating system, antivirus software on Androids, iPhones and other applications to patch security vulnerabilities and protect against the latest threats.
- Create strong passwords for your accounts and avoid reusing them across multiple platforms. Consider using a password manager to securely store and generate complex passwords.
- BBe wary of suspicious emails, messages, or links that ask for personal information or login credentials. Verify the legitimacy of the sender before clicking on any links or providing sensitive data.
- Use encryption tools or features to encrypt sensitive files and documents stored on your devices or when transmitting them over the internet. This ensures that even if your data is compromised, it remains unreadable without the decryption key.
- Change the default password on your home router, enable encryption (WPA2 or WPA3), and use a strong network password to protect your home network from unauthorized access.
- Utilize encrypted messaging and video conferencing tools that prioritize privacy and data security, especially when discussing sensitive information.
- Implement a regular backup strategy for your important files and data. Use secure cloud storage or external hard drives to create backups, ensuring that you have a copy in case of data loss or ransomware attacks.
- Stay informed about the latest threats, scams, and security practices through reputable sources. Continuously educate yourself about potential risks and how to mitigate them.
- Keep your devices physically secure by locking them when not in use and avoiding leaving them unattended in public places. Use biometric authentication or strong passwords to prevent unauthorized access.
- If you're working for an organization, familiarize yourself with their data security policies and guidelines. Follow their recommended practices to ensure compliance and protect sensitive information.
Remember, data security is an ongoing effort, and it's essential to remain vigilant and proactive in safeguarding your information while working remotely.
Here are some practical easy things remote people can do to protect data.
#1.Follow a Cybersecurity Policy
Every company should have a cybersecurity policy so that every employee knows how to stay safe when working remotely.
While effective technologies and policies are beneficial, it is important to acknowledge that employees themselves pose a significant security risk to businesses.
Implementing general work-from-home and remote work policies that govern computer and internet usage can mitigate these risks. These policies should be reinforced through a combination of technical and administrative controls.
Promoting security awareness among employees is crucial for ensuring the safe handling of corporate devices and information, regardless of their location.
Chief Information Security Officers (CISOs) and IT managers can easily integrate these work-from-home security strategies into official employee and cybersecurity policies.
We recommend providing training on these policies during the onboarding process for new employees, as well as during recurring security awareness sessions.
It is essential to educate employees whenever updates are made to the company's security policies.
Also, training for workers will not be superfluous to consolidating knowledge about keeping data protected.
#2.Use Only Secure Connections
Most online workers in the US have set up their home offices. But 25% of remote employees prefer performing tasks from cafes and restaurants. Of course, any worker once in a while wants to enjoy that Starbucks cup of coffee, bringing a laptop to a public place.
That is where the data leak can happen: by either using free Wi-Fi, or even one with a password.
For hackers, this is a perfect possibility to gain access to your computer and all sensitive data.
But using a virtual private network (VPN) can be a solution. VPN works as an intermediary and encrypts requests sent to a server. Browsers like DuckDuckGo use encryption and anonymization features to help protect your online privacy.
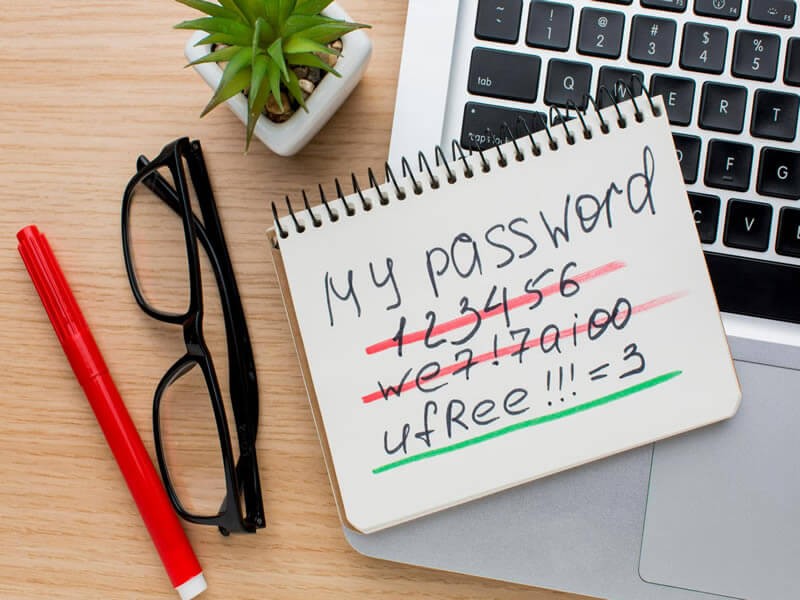
#3.Create Strong Passwords
The most basic yet very important practice is to have accounts with strong passwords. Attackers usually use a brute-force attack, which means they are trying different passwords until they guess the right one.
And if you have the same login credentials for several accounts, you become endangered that all your accounts will be hacked.
The recommendations for creating a solid password are the following:
- It should consist of a minimum of 12 characters (but the more, the better).
- There should be uppercase and lowercase letters.
- It should include special characters like #, *, №, and so on.
- It should contain numbers.
A helpful tool for creating strong passwords is a password manager. It will automatically generate a random set of letters, numbers, and characters, and then store it in an encrypted vault.
#4.Set Two-Factor Authentication
A strong password is not enough to ensure data security while working remotely.
For better protection, use two-factor authentication (2FA). After you write your credentials, the system will send you a code to your phone which is more difficult to gain access to.
Along with 2FA, you can add extra layers of protection.
They can be biometric authentication (facial recognition, voice recognition, fingerprint scanner), Captcha tests, certificate-based recognition, or token-based authentication.
#5.Implement Zero Trust Network Access
An approach that zero-trust network access (ZTNA) supports is that every resource or channel before entering is checked for legitimacy. Only after the system authenticates that the service is not malicious, the user can get access to it.
With ZTNA, every web address you enter is secure. Before you access any platform, the system makes an outbound connection with no data exposure.
Hackers will not be able to see your IP address or other data.
#6.Make a Risk Assessment
Conducting a risk assessment can help highlight those points that don't allow a company to be totally sure of data protection. The procedure is held by third parties which check your system for vulnerability. The security professionals will tell you where to focus more attention and teach employees how to be safe.
Wrapping up
Security is the main factor every remote worker should be mindful of. While you think that you are not an interesting object for hackers, they think you are. To avoid being a victim of cybercrime, it is essential to follow the strategies for protecting sensitive data.
They include sticking to a cybersecurity policy, using secure connections, creating strong passwords, setting extra layers of authentication, using zero-trust network access, and conducting risk assessments.
Categories
Blog
(2934)
Business Management
(365)
Employee Engagement
(222)
Digital Transformation
(190)
Growth
(140)
Intranets
(134)
Remote Work
(63)
Sales
(53)
Collaboration
(47)
Customer Experience
(30)
Culture
(29)
Knowledge Management
(28)
Project management
(28)
Leadership
(20)
Comparisons
(9)
News
(1)
Ready to learn more? 👍
One platform to optimize, manage and track all of your teams. Your new digital workplace is a click away. 🚀
Free for 14 days, no credit card required.